
Amazons GPT55X Unveiled
Hey there, tech enthusiast! 🚀 Grab your coffee because we're about to dive into one of the most exciting innovations ...

The Essential Guide to Mastering Local SEO
Introduction to Local SEO Search Engine Optimization (SEO) is vital for businesses to get noticed in the vast online marketplace ...

How to Make an Enchanting Encanto Cake at Home
Disney's vibrant animation, Encanto, with its captivating characters and colorful visuals, serves as a fantastic inspiration for creating a magical ...

Encanto Cake Ideas
If you're as enchanted by Disney's colorful animation Encanto as we are, you'll love these creative and delicious Encanto cake ...

Disney-Themed Pumpkin Painting
As the autumnal winds blow in, there’s something magical about the season that sparks creativity in every corner, especially when ...

Disney Pumpkin Painting Ideas
Fall is the perfect time to explore your artistic side with some pumpkin decorating. If you're a Disney lover, there's ...
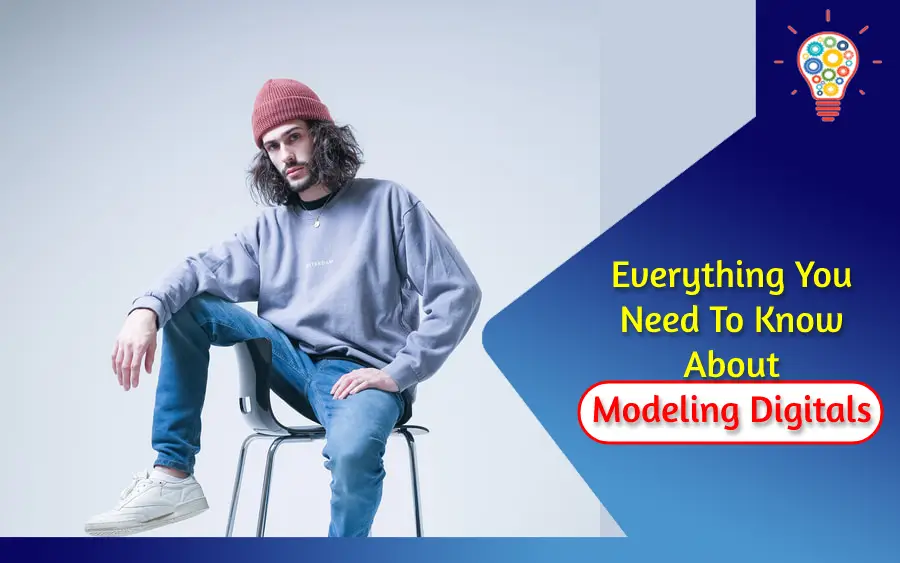
Everything You Need To Know About Modeling Digitals
Today we're talking about among the most important aspects of your portfolio: Modeling Digitals Whether you're simply starting in the ...

Digital Screen Print Transfer Printers
Introduction to Digital Screen Print Transfer Printers 1.1. What is Digital Screen Print Transfer Printing? Digital screen print transfer printing ...

Difference Between iPhone 12 Pro max vs iPhone 14 Pro Max
The iPhone 12 Pro Max and iPhone 14 Pro Max are two of the latest and most advanced smartphones from ...

Carbide Tillage Tools – Maximizing Efficiency and Precision in Farming
Carbide tillage tools are agricultural implements designed to break up, loosen, and manipulate the soil in fields and gardens. These ...
David Dobrik Net Worth: From Vine Sensation to YouTube Magnate
Have you ever found yourself deep-diving into the vast world of YouTube and stumbled upon David Dobrik? If his name ...

5 Ways to Re-Engage Dissatisfied Employees
What keeps you up at night as a business owner? Is it the fear of losing clients, falling behind the ...

Strengthening Your Data Defense: Personal and Business Strategies
Key Takeaways Understanding the importance of personal and business data privacy. Exploring practical measures for enhancing information security. Providing insights ...

What is brainwriting: A quick guide to boost creative collaboration
Imagine walking into a room where the air buzzes with creativity, and everyone is eager to innovate. That's the power ...

Accessorizing with Time: The Role of Watches in Men’s Fashion
From the boardroom to the boat deck, a watch has traditionally denoted a sense of style and an appreciation for ...

Unpacking the Costs and Perks of the Freedom Boat Club Membership
The Freedom Boat Club might just be the gold standard when it comes to boating clubs in the U.S., and ...





